When you send Bitcoin from one wallet to another, the whole world can see it. Not just the amount, but exactly which wallet sent it and which one received it. That’s the truth of blockchain-it’s public, permanent, and traceable. But what if someone wanted to hide that trail? That’s where cryptocurrency mixing services come in. And for countries like North Korea, these tools aren’t just about privacy-they’re a lifeline for laundering stolen money.
How Cryptocurrency Mixers Work
Cryptocurrency mixers, sometimes called tumblers, don’t create new money. They just make it harder to follow where the money came from. Think of it like this: you and nine other people each put $100 in a big jar. The mixer shuffles all the bills, then gives each of you back $100-but not your original bills. Now, no one can say which dollar was yours. That’s the whole point.
The process is simple but effective:
- You send your cryptocurrency to the mixer’s address.
- The mixer pools your coins with hundreds or thousands of others.
- It shuffles them using complex algorithms or smart contracts.
- After a delay, it sends back the same amount to a new address you control.
Most mixers charge a fee-usually 1% to 3%-to cover costs and make a profit. But the real danger isn’t the fee. It’s that this process breaks the link between the original sender and the final receiver. And for criminals, that’s gold.
Centralized vs. Decentralized Mixers
Not all mixers are built the same. There are two main types, and they carry very different risks.
Centralized mixers are the old-school kind. You send your coins to a company, they hold them in their wallet, mix them up, and send them back. It sounds easy-but you’re trusting a single company with your money. And history shows that’s risky. Operators have vanished with millions. Others got hacked. Some even kept logs of who sent what, meaning if law enforcement ever got their hands on those records, every user’s privacy was gone.
Decentralized mixers work differently. They use smart contracts on blockchains like Ethereum. No company owns or controls the process. Instead, multiple users pool their coins into a contract that automatically shuffles them using cryptography-like CoinJoin or ZK-SNARKs. No one holds your coins. No one keeps logs. The system does the work, and you keep control. These are harder to shut down and far more private.
But here’s the catch: decentralized mixers still need users. The more people join, the harder it is to trace any single transaction. That’s why North Korea’s hackers don’t just use one mixer-they flood multiple systems with small transactions to blend in.

North Korea’s Crypto Laundering Machine
North Korea doesn’t have a banking system most of the world trusts. It can’t move money through SWIFT or Western banks. So it turned to crypto. And it got very good at it.
Since 2017, North Korean hacking groups like Lazarus have stolen over $3 billion in cryptocurrency from exchanges, DeFi protocols, and crypto firms. They didn’t just steal it. They cleaned it. And mixing services were their main tool.
Here’s how it works in practice:
- A hacker steals $5 million in Ethereum from a DeFi platform.
- They split it into 500 smaller transactions and send each to different centralized mixers.
- Each mixer shuffles the coins with others, then sends them to new addresses.
- Some of those outputs go through a second mixer-layering obfuscation.
- Finally, the funds are converted to Bitcoin, then cashed out through peer-to-peer traders in Southeast Asia or via crypto ATMs.
U.S. Treasury reports show North Korea used at least 12 different mixing services between 2020 and 2024. Some were well-known, like Blender.io (now shut down). Others were obscure, operated from servers in Vietnam or Russia. The goal wasn’t secrecy-it was noise. By overwhelming the system with small, mixed transactions, they made tracking impossible.
Why Law Enforcement Struggles
The U.S. Department of Justice has indicted operators of crypto mixers. In 2023, four Russians were charged for running Blender.io and Sinbad.io. But the case was weak. Prosecutors relied on forum posts and vague chat logs. They didn’t prove the operators knew they were helping North Korea. And that’s the legal gray zone.
Most mixers claim they’re just for privacy-conscious users-people in authoritarian regimes, journalists, or those worried about surveillance. And some of them are. But the same tools that protect dissidents also protect thieves. And regulators can’t easily tell the difference.
Even worse, decentralized mixers don’t have operators to arrest. No CEO. No headquarters. No bank account. Just code running on a blockchain. Shutting them down isn’t like closing a shop. It’s like trying to ban a mathematical formula.
The Global Crackdown
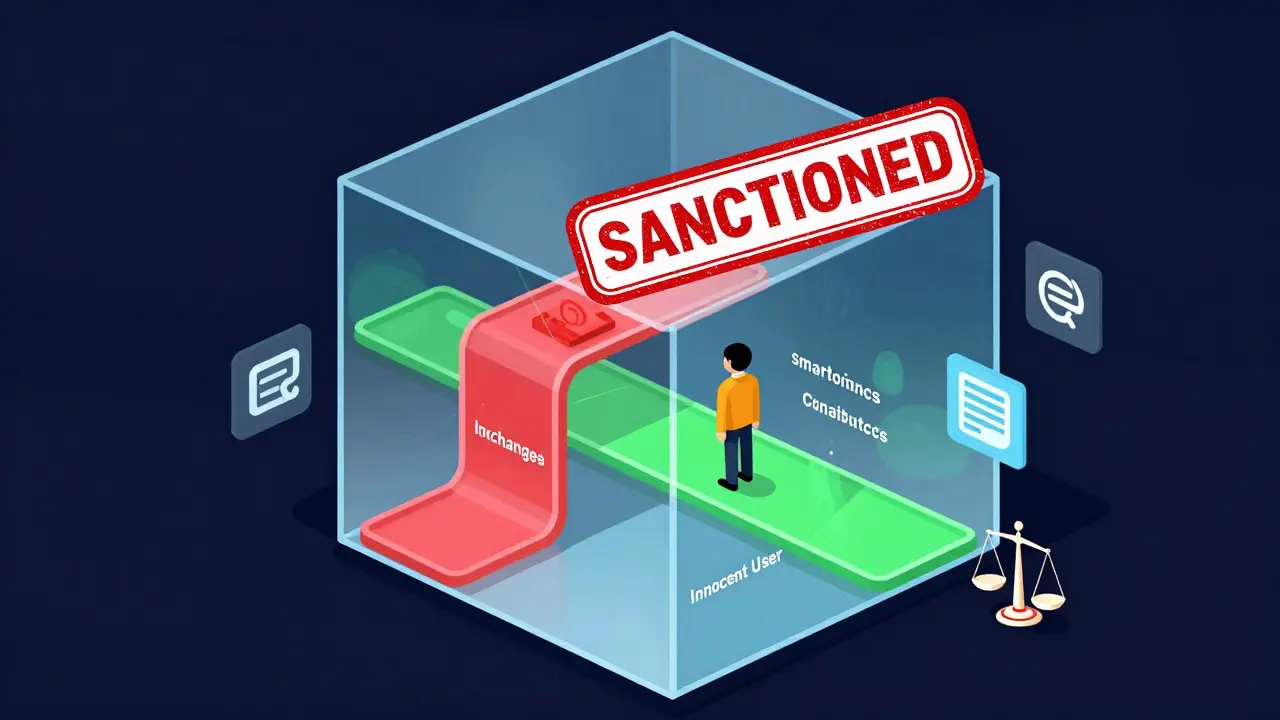
Financial regulators are catching on. The Financial Action Task Force (FATF), the global watchdog for anti-money laundering rules, now lists mixing services as high-risk. In 2025, the EU passed new rules requiring all crypto exchanges to block transactions from known mixing services. The U.S. Treasury added 17 mixer addresses to its sanctions list.
Exchanges like Binance, Coinbase, and Kraken now scan incoming transactions. If a coin passed through a mixer flagged by the U.S. or UN, it gets frozen. Some users have lost access to their funds because a single input came from a mixed transaction-even if they didn’t use the mixer themselves.
It’s a blunt tool. Innocent people get caught. But for North Korea, the cost of getting caught is lower than the cost of not laundering. They’ve built an entire economy around cyber theft. And mixing services are the grease that keeps it running.
The Bigger Picture
Cryptocurrency mixing isn’t inherently evil. It’s a tool. And tools can be used for good or bad. Privacy matters. People in China, Iran, or Venezuela have legitimate reasons to hide their transactions. But when a state actor weaponizes that privacy to fund nuclear weapons and missile programs, the line blurs.
The world is caught between two truths: blockchain should be transparent, but privacy is a right. And right now, the system is failing to balance them. Mixers are the symptom, not the cause. The real problem is that North Korea can steal billions and walk away clean-because the system wasn’t built to stop this.
Decentralized mixers aren’t going away. They’re getting better. And as long as there’s a demand for anonymity-whether from activists or dictators-these services will evolve. The only question is whether regulators can keep up.

Konakuze Christopher
March 19, 2026 AT 02:50They say mixers are for privacy, but let’s be real-this is just North Korea’s ATM network. They steal, mix, cash out, and laugh while the FBI chases ghosts. The whole system is rigged. Blockchain was supposed to be transparent, but now it’s just a magic trick with numbers. And we’re letting them win.
S F
March 19, 2026 AT 19:22Stop pretending this is about privacy. This is war. North Korea isn’t hiding money-they’re funding nukes. And every mixer that doesn’t get shut down is an act of treason. Time to burn the whole damn system down.
Angelica Stovall
March 21, 2026 AT 09:01Y’all think this is new? Nah. This is just crypto’s version of the old drug cartel money laundering. Only now, instead of suitcases full of cash, it’s smart contracts. And the government? They’re still asleep. Wake up people. This isn’t tech-it’s a heist.
Prakash Patel
March 22, 2026 AT 03:52Interesting take, but I wonder if the real issue is regulation, not the mixers themselves. Maybe the problem isn’t anonymity-it’s that we never defined what legitimate privacy looks like in crypto.
Elizabeth Kurtz
March 22, 2026 AT 21:02I’ve lived in three countries, and I’ve seen how people use tech to survive. In Iran, people use mixers to protect their savings from inflation. In Venezuela, to pay for medicine. It’s not all bad. But yeah, when a regime weaponizes it? That’s the dark flip side.
Ann Liu
March 23, 2026 AT 07:15Technically speaking, decentralized mixers like Wasabi Wallet and Samourai utilize CoinJoin protocols that aggregate inputs and outputs in a way that increases entropy, thereby reducing the probability of successful chain analysis. This is mathematically sound and not inherently malicious. The misuse by state actors is a governance failure, not a protocol flaw.
Jerry Panson
March 24, 2026 AT 04:40While I recognize the legitimate concerns regarding financial transparency and national security, I must emphasize that the indiscriminate freezing of all mixed transactions may constitute a violation of due process and property rights under U.S. constitutional principles. The remedy must be precise, not punitive.
Anastasia Danavath
March 25, 2026 AT 19:09So… mixers = bad? 🤡 I mean, if I wanna hide my crypto from my ex or my mom, is that a crime? 😅 Just saying…
anshika garg
March 27, 2026 AT 03:42It’s sad, really. We built this thing-blockchain-to give power back to the people. But now, the same tool that lets a refugee hide their last coins from a dictator also lets a regime buy missiles. Maybe the problem isn’t the tool… it’s us. We never decided who we were building it for.
Bruce Doucette
March 27, 2026 AT 19:30Oh wow, a whole essay on how North Korea uses crypto? Newsflash: they’ve been doing this since 2017. You think the U.S. government didn’t know? They just don’t care enough to stop it. This isn’t about tech-it’s about politics. And nobody’s got the balls to say it.
Marie Vernon
March 29, 2026 AT 01:34I get why people are scared. But let’s not punish everyone who wants privacy because a few bad actors are abusing it. We’ve done this before-remember when people said email was for spammers? We didn’t shut it down. We made better filters.
Billy Karna
March 30, 2026 AT 10:38Let’s break this down step by step. The economic isolation of North Korea since the 1990s forced them into asymmetric warfare, and cybercrime became their primary revenue stream. With traditional banking cut off, crypto offered a decentralized, borderless, and pseudonymous alternative. The use of mixers is not incidental-it’s strategic. They don’t just use one mixer; they cascade through multiple, layered, and often overlapping protocols, including both centralized and decentralized systems, to create transactional entropy that overwhelms chain analysis tools. This is not amateurish behavior; it’s a sophisticated, state-sponsored financial engineering operation that has evolved in real-time in response to global sanctions and monitoring efforts. The real failure isn’t the technology-it’s the regulatory lag. We’re still trying to apply 20th-century financial oversight to 21st-century decentralized networks. Until we update our frameworks, we’ll keep losing this game.
Cheri Farnsworth
March 31, 2026 AT 12:41Regulation must be proportional. Sanctioning entire protocols punishes innocent users. We need targeted intelligence, not blanket bans.
Gene Inoue
April 1, 2026 AT 17:41Oh look, another crypto bro pretending privacy is sacred. You think Kim Jong-un gives a shit about your ‘right to anonymity’? He’s stealing from you to fund missiles. Stop being naive. This isn’t a debate-it’s a war, and you’re on the wrong side.
Arlene Miles
April 3, 2026 AT 15:01It’s not about banning mixers-it’s about building better tools to trace the *pattern* of theft, not the *transaction*. If we focus on the hacker’s behavior-how they move funds, which exchanges they cash out at, which wallets they reuse-we can catch them without killing privacy for everyone else. It’s possible. We just need to stop being lazy.
Jessica Beadle
April 3, 2026 AT 16:27The FATF’s classification of mixers as high-risk is a logical extension of AML/CFT frameworks. The inherent design of coin aggregation protocols introduces non-deterministic transactional pathways that violate the Travel Rule’s core tenets. Furthermore, the use of ZK-SNARKs in newer decentralized implementations introduces computational irreducibility, rendering forensic analysis infeasible without quantum decryption capabilities. This constitutes an existential threat to global financial integrity.
Patty Atima
April 4, 2026 AT 12:53Hope we find a better way. 🤞
Lucy de Gruchy
April 6, 2026 AT 04:19Of course they use mixers. The real scandal is that the U.S. Treasury has sanctioned addresses but never taken down the servers. Why? Because they’re hosted in places the U.S. can’t touch. This isn’t about crypto-it’s about geopolitical impotence.
Carol Lueneburg
April 7, 2026 AT 12:50There’s beauty in tech that lets people stay safe. And there’s horror in how it’s twisted. Maybe we need two systems-one for transparency, one for privacy. Not one rule for everyone.
Brenda White
April 7, 2026 AT 20:43wait so if i use a mixer im a criminal? like what if i just dont want my boss to know i have crypto? 😭